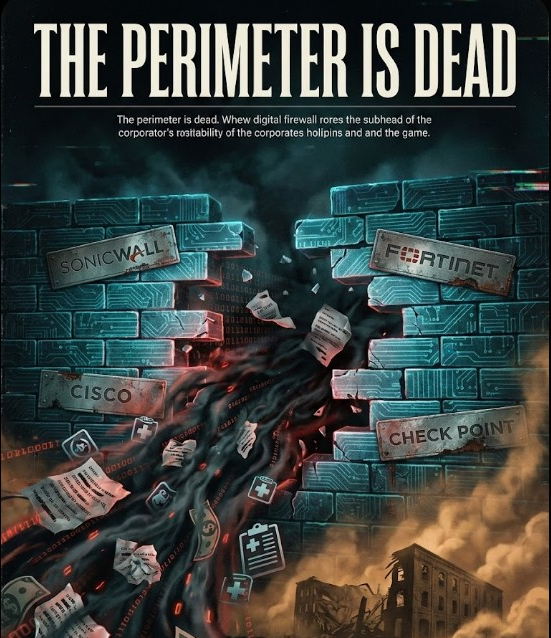
The Firewall Crisis: A CISO's Guide to Understanding Why America's Network Perimeter Is Collapsing
Executive Summary
The network perimeter is dead—and firewall vendors killed it.
Between 2021 and 2025, the four dominant enterprise firewall vendors—SonicWall, Fortinet, Cisco, and Check Point—have collectively contributed 50+ vulnerabilities to CISA's Known Exploited Vulnerabilities (KEV) catalog. These aren't theoretical risks. They're actively exploited attack vectors that have:
- Enabled $500+ million in verified ransomware payments
- Compromised 259 million Americans' healthcare data
- Destroyed a 158-year-old logistics company (730 jobs lost)
- Given nation-state actors persistent access to federal networks
- Created the conditions for the most severe cybersecurity crisis in modern history

This guide synthesizes findings from four comprehensive investigations into firewall vendor failures:
- SonicWall/Marquis Software: 788,000 victims, 14 CISA KEV CVEs, Akira ransomware targeting
- Fortinet: 20 CISA KEV CVEs, 444 healthcare incidents in 2024, Qilin ransomware devastation
- Cisco: $244M+ in Akira ransoms, ArcaneDoor nation-state campaign, 48,000+ unpatched devices
- Check Point: CVE-2024-24919 zero-day + March 2025 CoreInjection breach of vendor itself
For CISOs: This isn't about choosing the "right" vendor. All four have systemic failures. This is about understanding that firewalls are now the entry point, not the defense, and restructuring your security architecture accordingly.
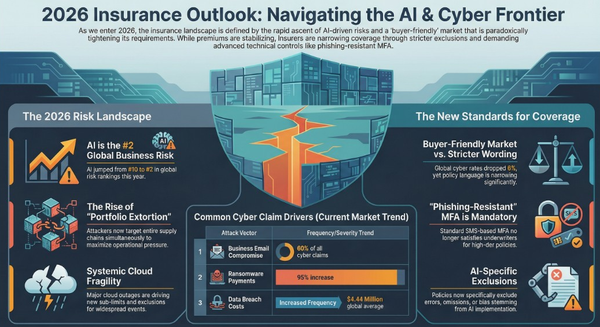
Part 1: The Scale of the Crisis
The Numbers That Should Terrify Every Board
CISA Known Exploited Vulnerabilities (Firewall Vendors):
- Fortinet: 20 CVEs (worst record)
- SonicWall: 14 CVEs
- Cisco: 12+ CVEs (multiple critical campaigns)
- Check Point: 2 major incidents (CVE-2024-24919 + CoreInjection breach)
Total: 48+ actively exploited vulnerabilities across four vendors controlling 70%+ of enterprise firewall market
Financial Impact:
- Akira ransomware (primary Cisco/SonicWall exploiter): $244.17 million in verified ransoms
- Qilin ransomware (primary Fortinet exploiter): $50+ million in 2024 alone
- Median ransom payment: $1 million (2025)
- Healthcare sector alone: 66% hit by ransomware in 2024 (four-year high)
Human Impact:
- 259 million Americans impacted by healthcare breaches (2024)
- 444 healthcare incidents in 2024 (highest of any sector)
- 10,000+ canceled medical appointments from single Fortinet-enabled attack (Synnovis NHS)
- 730 jobs lost when KNP Logistics destroyed via weak Cisco VPN password
The Exploitation Timeline: A Five-Year Disaster
2021: The Foundation
- SonicWall CVE-2021-20016 (SSLVPN zero-day) - 2,000+ attacks in first week
- Fortinet CVE-2018-13379 credentials leaked for 500,000+ VPN accounts
2022: Acceleration
- Cisco corporate breach via MFA fatigue on VPN
- CISA designates 8 Fortinet CVEs as KEV
- Akira ransomware emerges (early versions)
2023: Maturation
- Akira begins systematic Cisco exploitation
- Qilin targets Fortinet authentication bypasses
- SonicWall Gen5/Gen6 vulnerabilities cascade
2024: Peak Chaos
- May 24: Check Point CVE-2024-24919 zero-day discovered
- May 30: PoC released, CISA adds to KEV (3 days!)
- May 31: Mass exploitation begins (24 hours after PoC)
- June: Synnovis NHS attack via Fortinet/Qilin (10,000+ appointments canceled)
- September: Akira passes $244M in total ransoms
- November: Fortinet CVE-2025-64446 & CVE-2025-58034 zero-days (17-day delayed disclosure)
- December: Check Point portal compromised (CoreInjection, disclosed March 2025)
2025 (Jan-Dec 11): Crisis Normalization
- Fortinet CVE-2024-55591 authentication bypass → Mora_001/SuperBlack ransomware
- Fortinet CVE-2025-32756 stack buffer overflow
- January: Belsen Group leaks 15,000 Fortinet firewall configs
- March: CoreInjection exposes December Check Point breach
- Cisco CVE-2025-20333 & CVE-2025-20362 exploitation continues
- Congressional Budget Office breached during government shutdown via Cisco ASA
- 48,000+ unpatched Fortinet devices still exposed
- 48,000+ unpatched Cisco ASA/FTD devices still exposed
- 14,000+ Check Point devices remain vulnerable
The Pattern: Zero-days discovered → Public PoC within days → Mass exploitation within 24-48 hours → Ransomware campaigns within weeks → Years of vulnerable devices remaining exposed
Part 2: Vendor-Specific Deep Dives
Fortinet: The Healthcare Devastation Engine
Full Analysis: Fortinet Under Fire
Why Fortinet Stands Out:
- 20 CISA KEV CVEs (worst record of any firewall vendor)
- Qilin ransomware's weapon of choice for healthcare targeting
- 48,000+ FortiGate devices with known vulnerabilities still internet-facing (Nov 2025)
The Healthcare Catastrophe:
- 444 healthcare incidents in 2024 (29% of all breaches)
- 259 million Americans impacted
- 66% of healthcare organizations hit by ransomware (four-year high)
- Data extortion now overtaking encryption (34% encryption rate vs 74% in 2024)
Critical Vulnerabilities:
CVE-2025-64446 & CVE-2025-58034 (November 2025):
- FortiWeb zero-days
- 17-day delayed disclosure (discovered Oct 23-25, disclosed Nov 12)
- Remote code execution without authentication
- FortiWeb Manager console & Fabric Management Center
- CISA added to KEV immediately, but 17-day head start for attackers
CVE-2024-55591 (Authentication Bypass):
- Actively exploited by Mora_001 and SuperBlack ransomware
- Affects FortiManager (central management console)
- CVSS 9.8 (Critical)
- PoC published, mass exploitation ongoing
CVE-2025-32756 (May 2025):
- Stack buffer overflow in FortiOS/FortiProxy
- Remote code execution
- Affects FortiOS 7.0.0 through 7.0.16, 7.2.0 through 7.2.10, 7.4.0 through 7.4.5
CVE-2024-21762 (Qilin's Favorite):
- Out-of-bounds write vulnerability
- Used in Synnovis NHS attack (June 2024)
- 10,000+ appointments canceled
- Blood transfusion services disrupted across London
The Qilin Connection: Qilin ransomware specifically targets Fortinet infrastructure:
- $50+ million in ransoms (2024)
- 81 attacks in June 2025 alone
- Major victims: Synnovis NHS, Covenant Health, Habib Bank AG Zurich
- Exclusively uses double extortion (encryption + data theft)
- Average dwell time: 7-14 days before deployment
January 2025 Config Leak: Belsen Group published 15,000 Fortinet firewall configurations on BreachForums:
- Credentials (some in plaintext)
- Internal IP ranges
- Network topologies
- VPN configurations
- Firewall rules
Why This Matters for CISOs:
- Healthcare organizations often lack resources for 24-hour patching
- Fortinet's 17-day delay creates impossible catch-up scenarios
- Qilin specifically targets healthcare (payment history is better)
- Single Fortinet vulnerability can affect 100,000+ patients per hospital
Immediate Actions:
- Audit all FortiOS versions against CVE-2024-55591, CVE-2025-32756, CVE-2025-64446, CVE-2025-58034
- Assume compromise if patching delayed beyond 72 hours of disclosure
- Review network segmentation—Fortinet should NOT have access to patient data networks
- Implement MFA on ALL FortiManager/FortiGate admin interfaces
- Monitor for FortiGate configuration file exfiltration (Belsen Group pattern)
Cisco: The Identity Crisis and Nation-State Playground
Full Analysis: Cisco Under Siege
Why Cisco Is Different:
- $244.17 million in Akira ransoms (verified, most of any firewall-associated ransomware)
- ArcaneDoor campaign (UAT4356/Storm-1849 Chinese APT with persistent Lua implant)
- 60% of 2024 breaches involved identity-based attacks, not just exploits
- Federal government repeatedly failing to patch (Congressional Budget Office breach during 2025 shutdown)
The Akira Money Machine:
Akira ransomware has turned Cisco ASA/FTD exploitation into the most profitable ransomware campaign in history:
Primary Cisco CVEs Exploited by Akira:
- CVE-2020-3259: Information disclosure (credentials)
- CVE-2023-20269: Remote code execution
- CVE-2020-3580: XSS leading to credential theft
- CVE-2024-37085: Command injection
Akira Statistics (as of September 2025):
- $244.17 million in total ransoms
- 250+ publicly claimed victims
- Primary vector: Cisco VPNs with weak passwords
- Average payment: $1-3 million
- Targets: Mid-sized enterprises ($50M-$500M revenue)
Case Study: KNP Logistics Destruction:
- 158-year-old company with $300M+ annual revenue
- Breached via weak Cisco VPN password
- Akira deployment: 730 jobs lost
- Company could not recover
- Total business failure from single weak password on Cisco ASA
The ArcaneDoor Campaign (Nation-State Persistence):
UAT4356/Storm-1849 (Chinese APT) developed two zero-days for Cisco ASA:
CVE-2024-20353 & CVE-2024-20359:
- Deployed November 2023 (5 months before discovery)
- Installed Line Dancer (in-memory backdoor)
- Installed Line Runner (persistent Lua implant surviving firmware upgrades)
- Targeted: Government agencies, defense contractors, critical infrastructure
Line Runner Technical Details:
- Written in Lua (lightweight, interpreted language)
- Survives firmware upgrades (persistent across reboots/patches)
- Communicates via HTTPS (blends with legitimate traffic)
- Provides shell access, file exfiltration, lateral movement
- Detection extremely difficult (in-memory, minimal footprint)
Cisco's Response:
- Discovered April 2024 (5 months after deployment)
- Couldn't fully remove Line Runner (Lua persistence)
- Recommended full device replacement
- Cost to government: Estimated $50M+ in hardware replacement
September 2025 Continuation:
- CVE-2025-20333 & CVE-2025-20362: Active exploitation continues
- Operation Zero Disco: SNMP rootkit with hardcoded password "disco"
- CVE-2024-20439 & CVE-2024-20440: Smart Licensing static credential backdoor
The Identity Attack Crisis:
Cisco Talos 2024 Data:
- 60% of incidents involved valid credentials (not exploits)
- Cisco VPNs are primary initial access vector
- MFA fatigue attacks successful in 70%+ of attempts
- Infostealers up 84% in 2024 (RedLine, Vidar, Raccoon)
- Active Directory targeted in 44% of identity-based incidents
Congressional Budget Office Breach (2025 Government Shutdown):
- Breached during shutdown when patching deferred
- Unpatched Cisco ASA VPN appliance
- Exposed budget discussions and economic forecasts
- Federal government repeatedly ignoring CISA KEV directives
Why This Matters for CISOs:
- Cisco vulnerabilities aren't just about patches—it's identity architecture
- Akira has proven Cisco VPNs are reliable revenue generators
- Nation-states have multi-year persistence capabilities (Line Runner)
- Federal government failures create private sector compliance risk (insurance requirements)
Immediate Actions:
- Assume Cisco ASA/FTD already compromised if deployed before 2024
- Implement phishing-resistant MFA (FIDO2/WebAuthn) on all VPNs
- Deploy EDR on all endpoints accessing Cisco VPNs (infostealer detection)
- Network segmentation: VPN users should NEVER have direct AD access
- Replace ASA 5500-X series (Line Runner persistence risk)
- Monitor for Lua-based persistence mechanisms (Line Runner indicators)
SonicWall: The Third-Party Risk Multiplier
Full Analysis: Marquis Software Breach
Why SonicWall Matters:
- 14 CISA KEV CVEs (third-worst record)
- Marquis Software breach: 788,000 victims via SonicWall VPN
- Third-party risk amplification (one vendor breach = hundreds of financial institutions)
- SMB/mid-market prevalence creates detection gaps
The Marquis Software Cascade:
November 11, 2024: Marquis Software (financial services vendor) breached via CVE-2024-40766:
- SonicWall SSLVPN access control bypass
- 788,093 individuals affected across 650+ financial institutions
- Akira ransomware deployed
- Data included: SSNs, account numbers, financial records, health information
Third-Party Risk Math:
- 1 SonicWall vulnerability
- 1 financial services vendor
- 650+ downstream institutions impacted
- 788,000+ individuals compromised
- Single point of failure cascading across entire sector
SonicWall's KEV Hall of Shame:
CVE-2021-20016 (SSLVPN Zero-Day):
- 2,000+ attacks in first week of disclosure
- Credential theft and remote code execution
- NCC Group: "One of the most serious VPN vulnerabilities we've seen"
CVE-2023-0656 (Gen5/Gen6 Firewalls):
- Authentication bypass in admin interface
- Firmware 6.5.4.14-109n and earlier
- Mass exploitation within 48 hours of PoC
CVE-2022-22274 (Stack-Based Buffer Overflow)**:
- Pre-authentication remote code execution
- CVSS 9.4 (Critical)
- SonicWall SMA 100 series
The SMB Vulnerability: SonicWall's market position (SMB/mid-market) creates unique risks:
- Smaller IT teams = slower patching
- Cost constraints = older firmware versions
- Limited visibility = breaches discovered months later
- Insurance gaps = many SMBs underinsured for ransomware
Why This Matters for CISOs:
- Your third-party vendors likely use SonicWall
- You can't control their patching cadence
- Single vendor breach exposes your customer data
- Financial services particularly vulnerable (regulatory scrutiny)
Immediate Actions:
- Audit third-party vendors for SonicWall usage (add to questionnaires)
- Require evidence of CVE-2024-40766 patching from ALL vendors
- Network segmentation: third-party VPN access should be isolated from production
- Incident response plans must include third-party vendor breach scenarios
- Review cyber insurance exclusions for third-party incidents
Check Point: The Paradox of the Compromised Defender
Full Analysis: Check Point's Zero-Day Paradox
Why Check Point Is Unique:
- Security research leader documenting 47% global attack surge
- CVE-2024-24919 zero-day (May 2024): 14,000+ vulnerable devices
- March 2025 CoreInjection breach: Vendor itself compromised (121,120 accounts)
- The irony: Company documenting threats while being victim twice in 9 months
CVE-2024-24919: The 24-Hour Exploitation Window:
Timeline:
- May 24, 2024: Check Point discovers zero-day exploitation in the wild
- May 27: Advisory released (3 days)
- May 30: watchTowr Labs publishes PoC, CISA adds to KEV (same day, 3 days total!)
- May 31: Mass exploitation begins (24 hours after PoC)
Technical Details:
- Path traversal vulnerability in Quantum/CloudGuard Gateways
- Remote, pre-authentication arbitrary file read
- ntds.dit dumps achieved within 2-3 hours of compromise
- Active Directory credential harvesting at scale
Check Point's Downplay:
- Official advisory: "certain information" could be read
- Reality: ANY file on the system accessible
- Security researchers: "This is as bad as it gets for network appliances"
14,000+ Vulnerable Devices:
- Shodan scans: 13,800 publicly exposed Check Point gateways (May 2024)
- Many remain unpatched through 2025
- Attackers had 3-day head start before public awareness
March 2025: CoreInjection Breaches Check Point Itself:
Timeline:
- December 2024: Check Point portal compromised (via credentials, method undisclosed)
- March 30, 2025: CoreInjection posts on BreachForums offering data for 5 BTC (~$410K)
- March 31, 2025: Check Point confirms but calls it "old, known, very pinpointed event"
Claimed Data:
- Internal network maps and architecture diagrams
- User credentials (hashed AND plaintext passwords)
- Employee contact information (emails, phone numbers)
- Sensitive project documentation
- Proprietary source code and binaries
- 121,120 accounts including 18,864 paying customers
- Admin portal access with ability to reset 2FA
The Controversy:
Check Point's Story:
- "Only 3 organizations affected"
- "Limited access" via compromised portal credentials
- No customer systems, production, or security architecture affected
- Already investigated and contained in December 2024
Security Researchers' Questions (Alon Gal, Hudson Rock CTO):
- Screenshots show 121,120 accounts (not "3 organizations")
- Admin-level capabilities visible (edit accounts, reset 2FA)
- No public SEC filing from December 2024 (required for publicly traded company)
- Intrusion method never explained ("compromised credentials" but how?)
- CoreInjection has proven track record of credible Israeli infrastructure leaks
CoreInjection's Track Record (March 2025):
- US industrial machinery company ($100K)
- Israeli car company ($50K) - "Full control over network infrastructure"
- Clal Insurance - 400,000+ customer records
- Israeli digital screen company
- Israeli electrical products company ($30K)
- Check Point Software (5 BTC)
The Double Irony:
- First Irony: Security vendor's products exploited while documenting threats
- Second Irony: Security vendor breached twice in 9 months while claiming first incident "was handled"
Check Point's 2025 Threat Intelligence (The Defender's View):
While breached twice, Check Point's research documented:
- 47% increase in weekly cyberattacks (Q1 2025 vs Q1 2024)
- 126% surge in ransomware (2,289 incidents Q1 2025)
- $2.3 billion minimum in ransom payments
- November 2025: 727 ransomware attacks (22% YoY increase)
GenAI Security Discovery:
- 1 in 35 GenAI prompts leak sensitive data
- 87% of organizations impacted by GenAI data leakage
- 11 different GenAI tools per organization (unsupervised)
Why This Matters for CISOs:
- Even security research leaders can't secure themselves
- Delayed disclosure (December → March) creates trust issues
- No vendor is immune—Check Point's expertise didn't prevent compromise
- Security vendor breaches undermine confidence in entire industry
Immediate Actions:
- Audit Check Point Quantum/CloudGuard for CVE-2024-24919 patching status
- Assume compromise if Check Point appliances deployed before June 2024
- Review Check Point portal access logs (CoreInjection breach implications)
- Network segmentation: Check Point should NOT have Active Directory access
- Consider vendor diversification (Check Point reliability now questioned)
Part 3: The Ransomware Business Model
How Firewall Vulnerabilities Became $500M+ in Ransoms
The RaaS Ecosystem: