NSA and Cyber Command Nominee Faces Senate Scrutiny Over Technical Experience

Lt. Gen. Joshua Rudd defends unconventional background as concerns mount over critical cybersecurity leadership vacuum
The Trump administration's nominee to lead two of America's most critical cybersecurity organizations faced pointed questions Thursday about his lack of traditional digital warfare credentials, highlighting ongoing tensions over how to select leaders for rapidly evolving cyber operations.
Army Lt. Gen. Joshua Rudd appeared before the Senate Armed Services Committee seeking confirmation as the next dual-hat commander of both U.S. Cyber Command and the National Security Agency. The three-star general, who spent most of his career in special operations rather than cyber or signals intelligence roles, argued his unique military background would prove sufficient for the demanding position.
The Experience Question
Rudd's nomination comes at a precarious moment for American cyber capabilities. Both organizations have operated without permanent leadership since far-right provocateur Laura Loomer initiated a campaign that successfully forced out the previous commander and reportedly contributed to the departure of several other senior officials. This leadership vacuum exists even as cyber threats from nation-states and criminal organizations continue escalating.
During his opening statement, Rudd attempted to reframe his qualifications: "For decades, I have had the opportunity to be a leader, consumer, enabler, generator and integrator of the intelligence and operational capabilities of NSA and Cyber Command." He emphasized his current role as deputy commander of U.S. Indo-Pacific Command, where signals intelligence and cyber capabilities factor into daily operational decisions.
The general's defense centered on his experience as a consumer and integrator of cyber and intelligence products rather than as a technical practitioner or cyber warfare specialist. "I'm confident that the incredible talent at CYBERCOM-NSA will provide great advice," Rudd told senators, suggesting he would rely heavily on existing technical expertise within the organizations.
Senate Concerns Surface
Not all lawmakers found this approach satisfactory. Sen. Angus King (I-ME) expressed particular frustration after Rudd provided non-committal answers about cyber deterrence strategy and policy.
"I'm confused because you're nominated to be the top cyber officer in the United States government, and you don't have any opinion on cyber policy," King said bluntly. "Are you simply a lever puller? I really don't understand, because this is a critical area of defense. It's a vector of attack on this country that's going on as we sit here today."
King's criticism underscores a fundamental debate in cybersecurity leadership: whether top positions require deep technical expertise or whether strategic military experience and leadership capabilities matter more. Traditional military leadership models often prioritize operational command experience over technical specialization, but cyber warfare's unique characteristics have challenged this assumption.
This debate extends beyond military positions to civilian cybersecurity leadership roles as well. As outlined in The Modern Chief Information Security Officer, today's security leaders must balance deep technical knowledge with executive-level decision-making and strategic business alignment.
The Dual-Hat Arrangement
Senators also pressed Rudd on the controversial shared leadership structure between Cyber Command and the NSA, a topic that has generated debate since the command's establishment. The arrangement places both organizations under single leadership, theoretically fostering integration between offensive cyber operations and signals intelligence gathering.
Rudd expressed support for the current structure based on his experience as a consumer, citing "effectiveness that fosters integration and speed." However, he notably hedged on future recommendations, promising to be "objective" and seek insights from both organizations and their customers about what works best.
This careful positioning suggests Rudd understands the political sensitivities surrounding potential organizational changes. Previous administrations have considered splitting the dual-hat arrangement, with proponents arguing each organization's distinct missions deserve dedicated leadership and opponents warning that separation would undermine operational synergies.
Workforce and Industry Engagement
On less controversial ground, Rudd committed to strengthening relationships with industry and academia to bolster the command's workforce pipeline. This emphasis addresses widely recognized talent shortages in government cybersecurity operations, where compensation and bureaucratic constraints make competing with private sector salaries increasingly difficult.
"Cyber is the domain that we're active in right now," Rudd acknowledged. "Some could say we're at war right now in that domain. I don't think that's an unfair characterization."
This framing—characterizing current cyber operations as warfare rather than peacetime competition—signals Rudd understands the operational tempo and threat environment he would inherit. China, Russia, Iran, and North Korea maintain sophisticated cyber capabilities that continuously probe American networks, steal intellectual property, and prepare infrastructure for potential conflict.
The challenge of attracting and retaining cyber talent remains acute across both government and private sectors. Organizations struggle to build effective security teams while facing a persistent cybersecurity skills shortage that represents a significant business and national security risk.
Political Realities and Confirmation Timeline
Despite questions about his qualifications, Rudd appears unlikely to face significant opposition from the Republican-controlled Senate. He will appear before the Senate Intelligence Committee later this month for additional questioning, but barring unexpected revelations or procedural holds, confirmation could occur within three weeks.
Current acting commander Army Lt. Gen. William Hartman is scheduled to retire in early February, creating urgency for Senate action. Extended vacancies in critical national security positions create continuity risks and can hamper long-term strategic planning.
Notably absent from Thursday's hearing were questions about recent high-profile military operations in Iran and Venezuela where Cyber Command has reportedly played significant roles. Senators focused almost exclusively on Rudd's qualifications rather than operational details or policy positions regarding cyber operations.
Implications for Cybersecurity Leadership
Rudd's nomination and the surrounding debate reflect broader questions about how America selects leaders for its cyber operations. Unlike traditional military domains where decades of doctrine and operational experience provide clear qualification standards, cyber warfare remains relatively new and rapidly evolving.
Some experts argue that strong leadership and the ability to integrate complex intelligence and operational capabilities matter more than hands-on technical experience at the four-star level. Others contend that cyber's unique characteristics—the speed of operations, technical complexity, and blurred lines between intelligence gathering and offensive action—demand leaders with deep domain expertise.
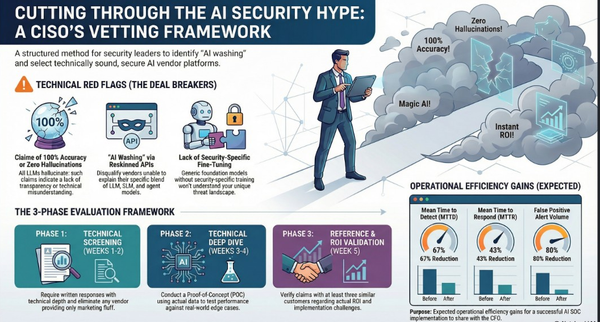
The selection criteria for top cybersecurity positions increasingly emphasizes a blend of capabilities. As documented in comprehensive CISO hiring guides, organizations now seek candidates who demonstrate both technical skills and soft skills including leadership, strategic thinking, and communication abilities.
The outcome may set precedents for future cyber leadership selections across the Department of Defense and Intelligence Community. If Rudd succeeds despite his unconventional background, it could validate the military's traditional leadership selection model. If he struggles, it might accelerate calls for specialized career paths for cyber officers similar to those that exist for other technical fields.
The Broader Context: Geopolitical Cyber Threats
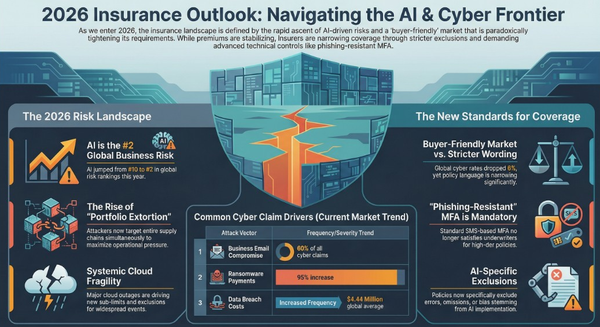
Rudd's nomination occurs against a backdrop of escalating cyber tensions. As explored in recent geopolitical analysis, organizations and nations face dual imperatives of defending against sophisticated attacks while navigating complex regulatory landscapes.
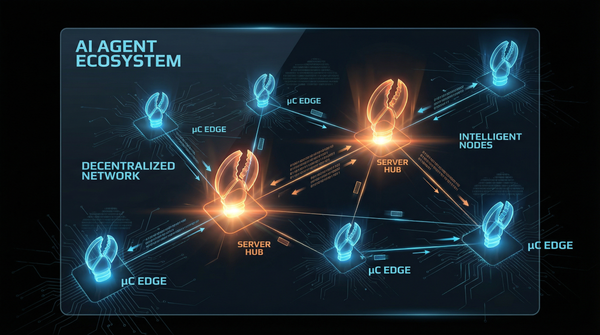
The convergence of cyber-physical systems has dissolved traditional security boundaries, creating new attack surfaces that span IT, operational technology, and IoT infrastructure. Nation-state actors increasingly target critical infrastructure, understanding that cyber operations can achieve strategic objectives without kinetic warfare.
This evolving threat landscape demands leaders who can bridge tactical operations and strategic vision—precisely the capability Rudd claims to bring from his special operations background. Whether that translates effectively to the cyber domain remains the Senate's central question.
What's at Stake
The NSA and Cyber Command positions represent two of the most consequential cybersecurity leadership roles in the world. The NSA operates as America's premier signals intelligence agency, collecting and analyzing communications intelligence critical to national security. Cyber Command conducts offensive and defensive operations in cyberspace, protecting military networks while degrading adversary capabilities.
Together under dual-hat leadership, these organizations must coordinate closely with allies, industry partners, and other government agencies. The commander shapes policy, sets operational priorities, and represents U.S. cyber capabilities in international forums. Poor leadership could compromise sensitive operations, erode partnerships, or leave vulnerabilities unexploited.
The role requires navigating sensitive political terrain, balancing civil liberties concerns with security imperatives, and managing complex bureaucratic structures across multiple agencies. Technical expertise matters, but so does political acumen, diplomatic skill, and the ability to communicate complex issues to policymakers who lack technical backgrounds.
Lessons for Civilian Cybersecurity Leadership
The debate surrounding Rudd's nomination offers insights relevant beyond military circles. Corporate boards and hiring managers face similar questions when selecting Chief Information Security Officers and other security leaders.
Should organizations prioritize candidates with deep technical backgrounds who rose through security operations centers and penetration testing teams? Or do leadership skills, business acumen, and strategic thinking matter more at executive levels where direct technical work becomes less frequent?
Modern CISO responsibilities extend far beyond technical implementation. Security executives must align programs with business objectives, communicate effectively with boards and executive teams, manage budgets and teams, navigate regulatory requirements, and maintain relationships with vendors and partners. Many successful CISOs come from non-traditional backgrounds, bringing fresh perspectives and cross-functional expertise.
Yet the technical foundation remains crucial. Security leaders must understand architectural decisions, evaluate security technologies, and recognize when technical teams need support or direction. Complete non-technical leaders risk becoming mere "lever pullers" disconnected from the realities of security operations—precisely Senator King's concern about Rudd.
The most effective approach likely involves hybrid models: leaders with sufficient technical background to understand core concepts, complemented by communication skills, business acumen, and strategic vision. Organizations should assess candidates holistically, considering how different strengths might serve specific organizational needs and contexts.
Looking Ahead
For now, the Senate appears poised to confirm Rudd and allow him to prove whether strategic military experience can substitute for technical specialization in leading America's cyber forces. The stakes could hardly be higher as adversaries continue advancing their own cyber capabilities and the digital threat landscape grows more dangerous.
If confirmed, Rudd will inherit organizations facing multiple challenges: maintaining technical superiority amid rapid technological change, competing for talent against well-funded private sector employers, balancing offensive capabilities with defensive imperatives, and coordinating across a complex interagency landscape.
His success or failure will likely influence not just future military cyber leadership selections, but broader debates about what qualifications matter most for security executives across all sectors. The cybersecurity community will watch closely, drawing lessons applicable to their own leadership development and hiring practices.
As cyber operations increasingly shape geopolitical outcomes and organizational success, getting leadership selection right becomes ever more critical. Rudd's nomination represents a test case for whether traditional military leadership models remain adequate for 21st-century cyber warfare—or whether the domain demands something fundamentally different.
Additional Resources
- Implementing Military-Style Cybersecurity Approaches - How organizations can adopt military-grade security practices
- The Modern CISO: Balancing Technical and Strategic Leadership - Comprehensive guide to contemporary security leadership
- Finding and Hiring Chief Information Security Officers - Best practices for CISO recruitment and evaluation
- Cyber Threat Intelligence as Executive Strategy - Leveraging intelligence for competitive advantage
- Geopolitics of Data: Compliance and Cyber Threats - Navigating global cyber threat landscape
What's your take on the technical expertise versus leadership experience debate for top cybersecurity positions? The tension between these approaches continues shaping how both government and private sector organizations select their security leaders, with implications that extend far beyond individual nominations.