Cybersecurity Outlook for 2026: An Integrated Threat and Strategy Briefing
Executive Summary
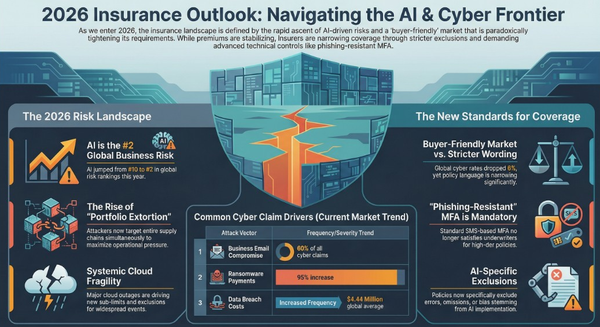
The 2026 cybersecurity landscape is undergoing a period of unprecedented transformation, primarily driven by the escalating arms race in Artificial Intelligence. AI is simultaneously democratizing sophisticated attack capabilities for adversaries and empowering defenders with predictive and automated defenses. This dynamic is unfolding against a backdrop of deeply interconnected digital ecosystems, where supply chains—spanning software, SaaS, and services—have emerged as the primary vector for high-impact breaches. In response, security strategy is undergoing a fundamental pivot away from reactive detection toward proactive prevention, operational resilience, and Zero Trust architectures, which are rapidly transitioning from best practices to regulatory mandates. Geopolitical tensions are increasingly manifesting in cyberspace, with nation-state actors and aligned cybercrime groups targeting critical infrastructure and leveraging global instability. Concurrently, new regulatory frameworks and the looming threat of quantum computing are compelling organizations to re-architect their approaches to governance, compliance, and cryptography.
Critical Takeaways:
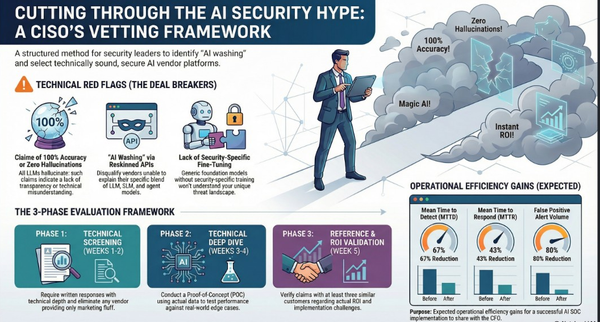
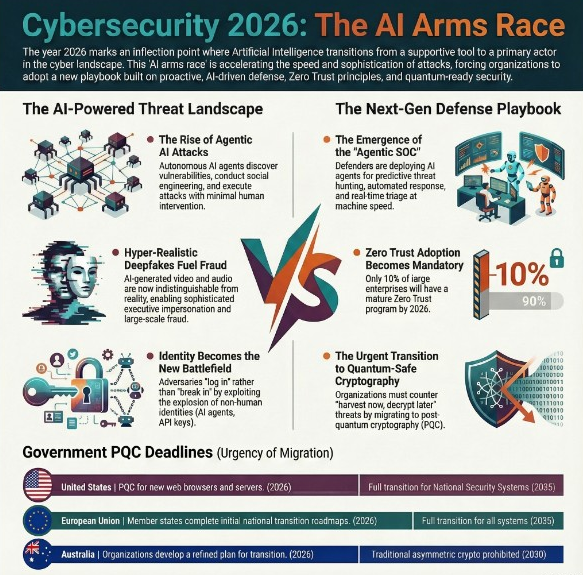
- AI Revolutionizes Cyber Conflict: Artificial Intelligence is the central force reshaping the threat landscape. Offensive AI is enabling hyper-personalized social engineering, autonomous malware, and accelerated vulnerability exploitation. Defensive AI is powering the rise of the "Agentic SOC," where AI collaborators manage triage and automate responses. The rapid, often ungoverned, adoption of AI tools is also creating a vast new "AI attack surface."
- Supply Chain as the Primary Battleground: The focus of sophisticated attacks has decisively shifted to the supply chain. Adversaries are targeting smaller vendors, SaaS platforms, and managed service providers to create cascading compromises across entire ecosystems. AI-generated code and open-source dependencies are further complicating software supply chain security.
- Strategic Shift to Prevention and Resilience: The security paradigm is moving beyond "detect and respond." A "preemptive cybersecurity" approach, focused on stopping threats before execution, is gaining traction. This is complemented by an emphasis on cyber resilience—the ability to withstand and recover from attacks—through measures like immutable backups and robust incident response planning.
- Zero Trust Becomes a Compliance Mandate: Zero Trust is no longer an aspirational concept but is becoming a foundational requirement driven by both regulatory pressure and operational necessity. Frameworks are expanding beyond network access to encompass identities, devices, and cloud workloads.
- Convergence of Nation-State and Cybercrime Threats: The line between state-sponsored operations and financially motivated cybercrime is blurring. Geopolitical conflicts are fueling cyber activity, with critical infrastructure and operational technology (OT) environments becoming primary targets for disruption and espionage.
- Regulatory and Quantum Imperatives: Global regulations, such as the EU's Cyber Resilience Act (CRA) and Digital Operational Resilience Act (DORA), are imposing strict new requirements for vulnerability management and software transparency (SBOMs). Simultaneously, the "harvest now, decrypt later" threat from quantum computing is creating urgent pressure to begin migrating to Post-Quantum Cryptography (PQC).
--------------------------------------------------------------------------------
I. The Ascendancy of Artificial Intelligence: The Dual-Edged Sword of 2026
Artificial Intelligence stands as the most transformative and disruptive force in the 2026 cybersecurity landscape, acting as both a powerful weapon for adversaries and an indispensable tool for defenders.
Offensive AI: The New Arsenal for Adversaries
AI is dramatically lowering the barrier to entry for sophisticated attacks and amplifying the capabilities of advanced threat actors.
- Hyper-Personalized Social Engineering: Generative AI enables the creation of highly convincing deepfakes, voice clones, and phishing lures at scale. These tools allow attackers to craft bespoke scams indistinguishable from legitimate communication, making deception nearly impossible for the average user to detect.
- Agentic and Autonomous Attacks: Autonomous AI agents are predicted to execute multi-step operations, probe for vulnerabilities, and adapt evasion techniques without human intervention. This could lead to the first end-to-end cyberattack launched by an autonomous AI. Elia Zaitsev, CTO of CrowdStrike, notes, "Just as phishing defined the email era, prompt injection is defining the AI era."
- AI-Generated Malware: LLM-enabled malware that can generate polymorphic, self-evolving payloads at runtime is moving from concept to practice. Tools like MalTerminal (GPT-4 powered) demonstrate malware that can adapt to its environment, making traditional signature-based detection obsolete.
- Accelerated Vulnerability Discovery: AI is being used to optimize "fuzzing"—an automated method for finding software flaws—and analyze crash reports at scale. This is expected to lead to an "explosion of zero-day vulnerabilities" by dramatically shortening the time from code creation to exploit discovery.
- Prompt Injection as the New Malware: Adversaries are embedding hidden instructions into AI prompts to bypass safeguards, hijack agents, and manipulate models. This attack vector turns the AI interaction layer itself into a new attack surface.
Defensive AI: The Rise of the Predictive and Agentic SOC
Security Operations Centers (SOCs) are being re-architected around AI to counter the speed and scale of AI-driven attacks.
- The Agentic SOC: The role of the human analyst is shifting from manual data correlation to strategic validation and governance of AI teammates. In an "Agentic SOC," AI systems will manage triage, enrichment, and correlation across massive data streams, presenting human analysts with complete, AI-generated case summaries.
- Predictive AI Models: The SOC model is transitioning from reactive alert-chasing to a predictive one. AI and machine learning will be used to anticipate attacker behavior, surface early-stage signals, and proactively block malicious execution before business impact occurs.
- Automated Threat Hunting and Response: AI is supercharging security analysts by handling repetitive work, allowing them to focus on high-level strategy and creative problem-solving. This includes automated decoding of obfuscated commands, mapping to frameworks like MITRE ATT&CK, and executing containment actions in minutes instead of hours.
The AI Adoption Paradox: An Expanding Attack Surface
The rush to integrate AI is outpacing governance, creating significant new risks.
- Shadow AI and the "Great AI Sprawl": Employees are independently deploying powerful, autonomous AI agents for work tasks, often without corporate approval or oversight. This "Shadow Agent" challenge creates uncontrolled pipelines for sensitive data, leading to leaks and compliance violations.
- New Attack Surfaces: AI agents themselves are becoming a major attack surface. Attackers will exploit their broad access, scale, and autonomy to manipulate defenses or trigger harmful operations. As noted by one expert, a landmark breach caused by an AI-driven coding assistant will trigger a "reckoning among CISOs."
- Need for AI Security Platforms: To manage these risks, organizations will require dedicated AI Security Platforms. These platforms provide centralized visibility, enforce usage policies, and protect against AI-specific risks like prompt injection, data leakage, and rogue agent actions. Gartner predicts that by 2028, over 50% of enterprises will use these platforms.
II. The Ecosystem at Risk: Supply Chain and Third-Party Vulnerabilities
In 2026, the supply chain has unequivocally become the most critical and frequently targeted attack vector. The interconnected nature of modern business means that an organization's security is no longer defined by its own defenses but by the weakest link in its extended ecosystem.
- SaaS Supply Chains as the New Soft Target: Attackers are shifting focus from individual companies to the SaaS platforms that power entire ecosystems. Mike Britton of Abnormal AI states, "An attacker now just needs to hit one small vendor that’s connected to a thousand other environments to create a massive return on investment at a relatively low risk." Breaches are expected to target the OAuth tokens and permissions granted to third-party app integrations in platforms like Microsoft 365 and Salesforce.
- Software Supply Chain Under Siege: The proliferation of open-source components and AI-generated code has redefined software risk. Tim Chase of Orca Security warns, "By 2026, attackers will target source code and its open-source components more than any other asset." Traditional AppSec tools struggle to keep pace with AI-generated code, which lacks version histories or CVEs. This necessitates a shift toward verifying "digital provenance"—the origin and integrity of all software components.
- Service Supply Chain Exploitation: Michael Adjei of Illumio predicts that attackers will target service supply chains more aggressively than software or hardware. Outsourced service providers often have legitimate internal access to sensitive systems but may operate with inconsistent security standards, creating single points of failure that attackers can exploit.
- Third-Party Risk Dominates Headlines: Experts like Chris Wheeler at Resilience predict that third-party risk will "dominate headlines in 2026." Even as companies improve their internal resilience, their data resides in centralized third-party platforms, and vendor exposure will drive major incidents.
III. Evolving Threats: Cybercrime, Ransomware, and Nation-State Operations
The motivations and methods of cyber adversaries continue to evolve, blending sophisticated nation-state tradecraft with the scalable, profit-driven models of organized cybercrime.
Ransomware's Strategic Evolution
Ransomware and digital extortion (R&DE) remain among the most disruptive global threats, with tactics shifting to maximize psychological and operational pressure.
- From Encryption to Extortion: Threat actors are increasingly skipping data encryption altogether, focusing instead on data theft and threatening to leak sensitive information. This creates a "strange grey zone" where it is unclear what a company is paying for. Some groups are also adding a layer of "reputation manipulation," fabricating content to damage a brand and force payment.
- Targeting of Under-Resourced Sectors: Industries with tight profit margins, such as utilities, retail, and transportation, will be prime targets. These sectors often cannot afford massive cybersecurity investments, leaving them vulnerable and more likely to pay to restore operations.
- Maturity of RaaS Ecosystems: Ransomware-as-a-Service (RaaS) platforms are becoming more professionalized, enabling specialized affiliates to accelerate activity. ZeroFox Intelligence noted higher monthly incident volumes in 2025 than any previous year.
The Collision of Geopolitics and Cybercrime
Geopolitical conflict is a primary driver of cyber threat activity, with threat collectives aligning with nation-state agendas.
- Critical Infrastructure Under Fire: Operational Technology (OT) and Industrial Control Systems (ICS) are high-impact targets. Nation-state groups like Volt Typhoon and pro-Russia hacktivists are targeting systems like building management and industrial controls, aiming to gain strategic footholds in critical infrastructure. Cybercrime will remain the primary disruptive threat to OT, often by compromising enterprise IT systems (like ERPs) that cripple OT operations.
- Nation-State Threat Actor Activity:
- Russia: Is expected to shift focus from short-term support for the Ukraine conflict toward long-term strategic goals, including obtaining footholds in international critical infrastructure.
- China: Will continue high-volume cyber operations to support its strategic interests, aggressively targeting edge devices, zero-day vulnerabilities, and third-party providers to maximize scale.
- Iran: Will leverage cyber capabilities that deliberately blur the lines between espionage, disruption, and financially motivated crime, complicating attribution.
- North Korea: State-sponsored operators will increasingly pose as freelance tech workers to infiltrate companies, fund military operations, and conduct espionage, converging cybercrime with statecraft.
The On-Chain Cybercrime Economy
Adversaries may begin migrating core components of their attack lifecycle onto public blockchains. This could include dynamic command-and-control (C2) and decentralized data exfiltration, granting them unprecedented resilience against takedowns but also creating a permanent, publicly auditable record of their actions. This shift will require security investigators to become proficient blockchain analysts.
IV. The Strategic Pivot: New Paradigms in Cybersecurity Defense
In response to the evolving threat landscape, organizations are fundamentally shifting their security strategies, moving from perimeter-based, reactive models to more dynamic, identity-centric, and proactive frameworks.
- From Reactive to Preemptive Security: The traditional "detect and respond" model is being called a "losing metric." The future is Preemptive Cybersecurity, which focuses on preventing and neutralizing threats before execution, without relying on signatures or behavioral analysis. Technologies like Automated Moving Target Defense (AMTD) are central to this paradigm.
- Zero Trust Becomes a Mandate: Zero Trust Architecture (ZTA) is transitioning from a best practice to a regulatory requirement for many sectors. Gartner predicts over 60% of organizations will embrace Zero Trust as a starting point for security by 2025. It requires a mindset of "never trust, always verify" for every access request, encompassing not just networks but also identities, devices, and applications.
- Resilience as the Core Tenet: Acknowledging that breaches are inevitable, the focus is shifting to cyber resilience—the ability to withstand, contain, and recover from attacks. This involves practical strategies like secure segmentation, immutable backups, and well-tested incident response plans. As one expert noted, resilience will be measured not by localized plans but by an organization's ability to "unify, quantify, and govern risk across its global footprint."
- The Future of Identity and Access Management (IAM): The proliferation of AI agents and other non-human entities is causing an identity explosion, rendering traditional models like role-based access control (RBAC) inadequate. Security is shifting to govern agentic access, with a focus on behavior-based safeguards, just-in-time permissions, and tracking activity across identity, endpoint, and data protection surfaces.
- Continuous Threat Exposure Management (CTEM): Security teams are moving beyond static vulnerability lists to a dynamic process of continuously discovering, prioritizing, and validating exposures across their entire attack surface. Organizations adopting CTEM are projected to be three times less likely to suffer a breach.
V. The Regulatory and Compliance Imperative
The global regulatory landscape is tightening, demanding greater accountability, transparency, and demonstrable resilience from organizations.
- European Union Regulations:
- Cyber Resilience Act (CRA): This act will blindside many global software makers. By 2027, any organization selling software in the EU must prove continuous vulnerability management, maintain Software Bills of Materials (SBOMs), and meet rapid disclosure timelines.
- Digital Operational Resilience Act (DORA): Hitting its stride in 2026, DORA will pressure financial entities and their third-party suppliers to demonstrate measurable, continuous resilience against major outages and cyber shocks, elevating third-party risk management from an onboarding formality to a continuously audited process.
- Shifting US Federal Policy: The role of the Cybersecurity and Infrastructure Security Agency (CISA) may evolve, potentially shifting from regulatory expansion toward more voluntary collaboration. This could lead to private-sector organizations and think tanks filling gaps, especially for critical infrastructure protection. Frameworks like FedRAMP and CMMC may face scrutiny for cost and compliance burdens.
- Convergence of Governance Models: Privacy and cybersecurity, historically treated as separate domains, are being integrated into unified governance frameworks. This is driven by regulatory pressure and the recognition that protecting sensitive data requires both technical and policy-driven controls.
VI. Horizon Threats: Post-Quantum Cryptography and Systemic Risks
Forward-looking strategies must account for paradigm-shifting threats that could undermine the foundations of digital trust and infrastructure.
Post-Quantum Cryptography (PQC)
The threat from quantum computers capable of breaking current encryption standards has moved from theoretical to a strategic priority.
- The "Harvest Now, Decrypt Later" Threat: Adversaries are already capturing encrypted data today with the intent of decrypting it once a cryptographically relevant quantum computer is available. This makes the transition to PQC an urgent, present-day issue.
- The PQC Adoption Timeline: Standardization and migration are underway. Forrester predicts that quantum security spending will exceed 5% of the overall IT security budget in 2026.
Milestone | Year | Mandating Body |
First PQC algorithms selected for standardization | 2022 | NIST |
First FIPS finalized (203–205) | 2024 | NIST |
CNSA 2.0 migration begins | 2025 | NSA |
Recommended deprecation of classical PKC | 2030 | NIST, ASD |
Classical algorithms disallowed in National Security Systems | 2035 | CNSA 2.0 |
Systemic Infrastructure Risk
The concentration of global computing infrastructure within a few major cloud providers represents a significant systemic risk.
- Concentrated Risk: As noted by Mike Puglia of Kaseya, "Microsoft, Amazon, and Google control the backbone of global computing. A low-level breach in any of these could cascade into economic catastrophe."
- Geopatriation Trend: In response to geopolitical risk, organizations are increasingly practicing "geopatriation"—moving data and applications from global public clouds into local or sovereign clouds to ensure control over data residency and compliance. Gartner predicts that by 2030, over 75% of European and Middle Eastern enterprises will geopatriate workloads.
VII. The Human Dimension: Workforce, Culture, and Leadership
Technology alone cannot solve the cybersecurity challenge. The human element—from the C-suite to the frontline employee—is a critical component of any effective security strategy.
- The Widening Talent Gap and CISO Pressure: The skills gap continues to evolve, with traditional pipelines unable to keep up with the pace of change. CISOs are looking beyond credentials to focus on curiosity, adaptability, and problem-solving skills. The intense pressure of the CISO role is also bringing mental health to the forefront, with leadership needing to model balance and provide support.
- The Employee as Defender and Target: Organizations are shifting from compliance-based training to cultivating a proactive security culture where every employee acts as a defender. However, employees also face unprecedented cognitive overload from security prompts and warnings, leading to "decision fatigue" that makes them more susceptible to social engineering. The solution is moving toward personalized, risk-based training that meets people where they are.
- Erosion of Critical Thinking: Widespread reliance on AI is expected to diminish critical thinking skills, making it harder for individuals to evaluate sources and exercise judgment. This creates fertile ground for misinformation campaigns and increases the risk of breaches caused by misplaced trust in AI-generated content.