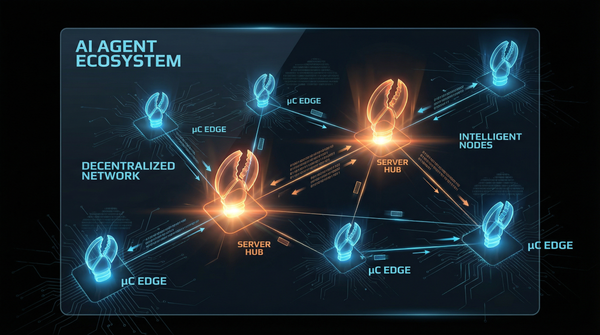
Briefing: An AI-Powered Ecosystem for Cybersecurity Policy Lifecycle Management
Executive Summary
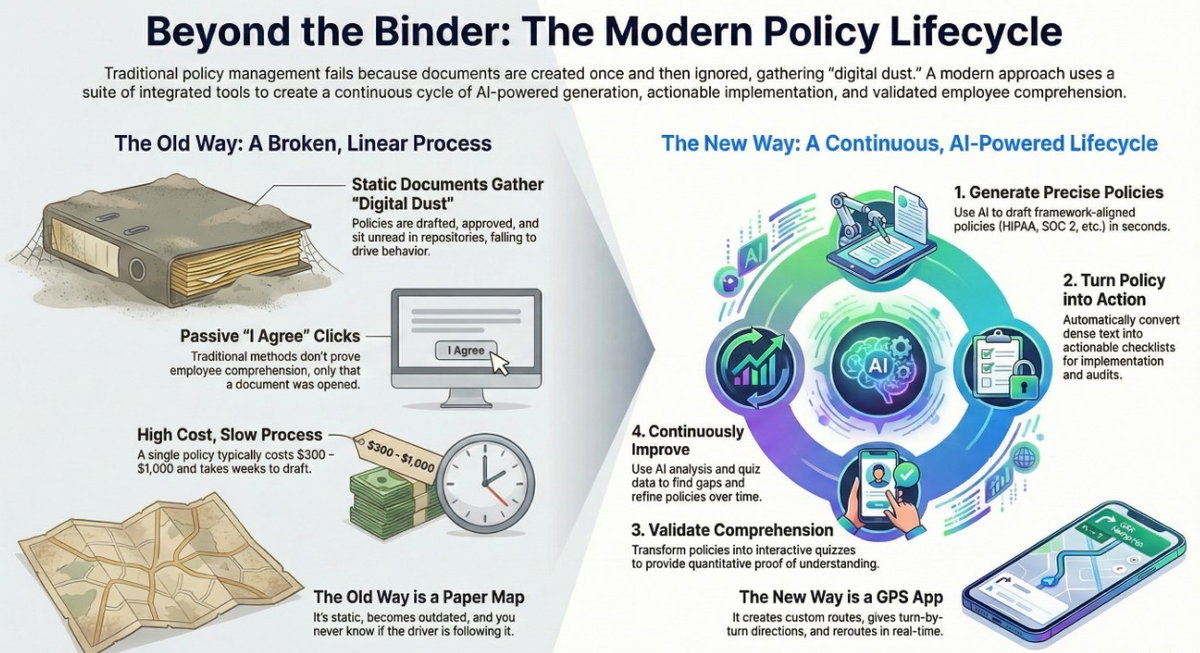
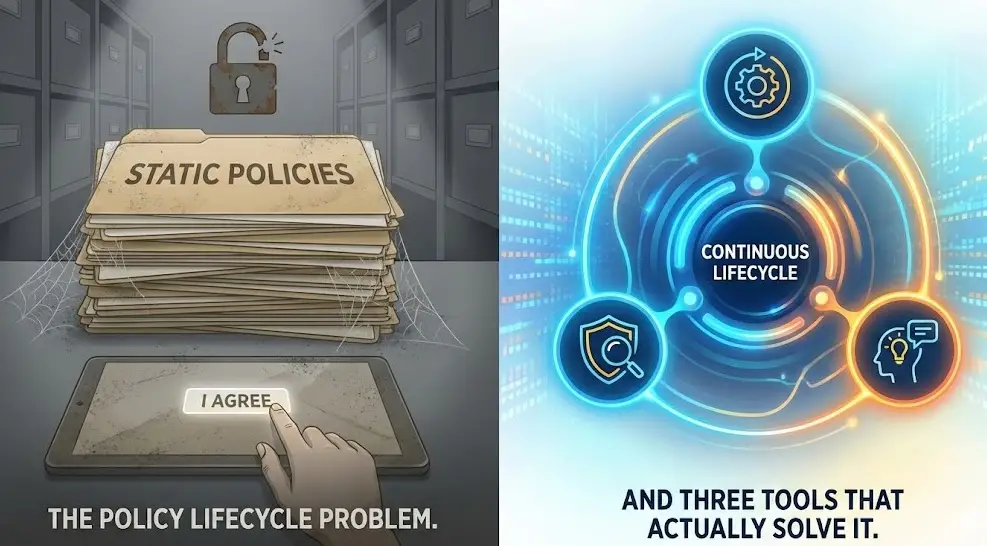
The traditional approach to managing cybersecurity policies—treating them as static, one-time documentation exercises—is fundamentally flawed, resulting in documents that gather "digital dust" and fail to drive meaningful security improvements. A new ecosystem of integrated, AI-powered tools addresses this failure by transforming policy management into a continuous, data-driven lifecycle. This ecosystem is built on three core pillars: precision generation, validation through engagement, and continuous improvement.
Central to this model is the use of AI to automate and enhance every stage. Platforms like GeneratePolicy.com and CyberTemplates leverage AI models such as Claude and Gemini 3 to draft framework-aligned security policies in seconds, drastically reducing costs compared to traditional consulting. To ensure these policies are operationalized, tools like SecureCheck and GeneratePolicy.com convert dense text into actionable checklists for IT teams and compliance questionnaires for auditors.
Crucially, the ecosystem solves the problem of employee comprehension. PolicyQuest.diy replaces passive "I agree" acknowledgments with interactive quizzes, providing quantitative evidence of understanding that is highly valued during audits. This data creates a feedback loop, identifying areas where policies are confusing and enabling continuous refinement. The result is a self-reinforcing cycle that improves audit efficiency, speeds up incident response, and makes continuous compliance an achievable goal.
The Policy Lifecycle Problem and the AI-Driven Solution
Standard organizational practice has long treated security policy management as a project with a defined end, leading to several critical failures. Policies are drafted, approved, and published to a repository, but their actual impact is rarely measured. This results in documents that are not understood by employees, contain outdated controls, and ultimately fail to reduce organizational risk.
An effective policy management strategy must be treated as a continuous lifecycle encompassing three distinct stages:
- Generation with Precision: Policies must be aligned with specific regulatory frameworks (e.g., SOC 2, HIPAA, GDPR) while also reflecting an organization's actual technical environment and risk profile. Generic templates often miss this crucial context.
- Validation Through Engagement: A policy's effectiveness depends entirely on whether it is understood and followed. Passive acknowledgments are insufficient; true validation requires testing employee comprehension to identify and close knowledge gaps.
- Continuous Improvement: The security landscape and regulatory requirements evolve rapidly. Policies require regular review and updates to remain relevant and effective against emerging threats.
An integrated suite of specialized tools has emerged to address these stages, creating a comprehensive solution for the modern compliance team.
Core Components of the Ecosystem
The policy lifecycle is supported by a set of interconnected platforms, each designed for a specific stage of the process, from initial creation to ongoing validation and refinement.
GeneratePolicy.com: The AI Policy Generator
GeneratePolicy.com is an AI-powered platform for the rapid creation of security and compliance policies. It is designed to solve the "cold start problem" for compliance programs.
- Technology: Powered by the Claude AI model.
- Capabilities: Generates new security policies, translates existing ones, and creates supplementary documents like implementation checklists and compliance questionnaires.
- Frameworks: Supports a wide range of global compliance standards, including HIPAA, GDPR, SOC 2, ISO 27001, NIST, PCI-DSS, CCPA, and FedRAMP, with access to over 368 professionally crafted templates.
- Features:
- Multilingual Support: Offers free translation into 12 languages, including English, Spanish, French, German, Chinese, and Japanese.
- Free Regeneration: Allows users to regenerate a policy based on feedback at no additional cost.
- Reward System: Users can earn tokens by providing feedback on generated policies.
- Zero Human Intervention: The platform is fully automated and available 24/7.
- Pricing Model: A flexible, token-based system where users purchase tokens and spend them on specific actions. New users receive 25 free tokens.
Action | Token Cost | Description |
Generate Policy | 10 tokens | Generate a new security or compliance policy. |
Generate Checklist | 3 tokens | Turn a policy into actionable implementation steps. |
Generate Questionnaire | 3 tokens | Create a compliance assessment questionnaire for audits. |
Translate Policy | FREE | Translate any policy to 12 supported languages. |
Regenerate Policy | FREE | Improve a policy based on user feedback. |
SecureCheck: The Dedicated Checklist and Workflow Platform
While GeneratePolicy.com offers checklists as an add-on, SecureCheck is a specialized platform focused on operationalizing policies and managing compliance workflows for IT teams and Chief Information Security Officers (CISOs).
- Primary Function: To convert existing security policies (from any source, including human-written ones) into step-by-step, actionable checklists using its "Policy to Checklist Converter."
- Features:
- Framework Alignment: Checklists are explicitly mapped to standards like SOC 2, NIST, and ISO 27001 for robust compliance tracking.
- Curated Templates: Includes a library of expert-crafted templates for various roles, such as executives and developers.
- AI Checklist Generation: Can create custom checklists tailored to specific organizational needs.
- Pricing Model: A subscription-based model offering unlimited use.
- Monthly Plan: $24 per month for full access to all features.
- Annual Plan: $230.40 per year, providing a 20% discount.
PolicyQuest.diy: The Comprehension and Validation Tool
PolicyQuest.diy addresses the critical validation stage of the lifecycle by transforming static policy documents into interactive learning and analysis tools.
- Primary Function: To test and validate employee understanding of security policies.
- Capabilities:
- Interactive Quizzes: Users paste policy text, and the AI instantly generates engaging multiple-choice questions and "scavenger hunts." This replaces passive "I agree" clicks with active verification.
- AI-Powered Analysis: The platform reviews policy text against industry best practices and modern security principles to identify gaps and suggest improvements.
- Effortless Merging: AI-suggested improvements can be consolidated with the original policy text into a new, updated document with a single click.
- Value Proposition: Provides auditors with "quantitative evidence of policy comprehension" and helps organizations identify and close knowledge gaps revealed by quiz analytics.
CyberTemplates & CyberPolicy.shop: Document Libraries
For organizations that prefer pre-written documents or need to supplement their AI-generated policies, two platforms serve as comprehensive libraries.
- CyberTemplates: An enterprise-focused platform using the Gemini 3 AI model to generate documents aligned with NIST, ISO 27001, SOC 2, and HIPAA. It offers over 600 templates and supports over 30 languages.
- CyberPolicy.shop: A digital marketplace offering professionally written, ready-to-use security policies and templates as digital downloads in PDF and JSON formats. This is positioned as a "no AI generation needed" option for teams needing specific documents quickly.
Key Functional Capabilities Across the Ecosystem
The synergy between the platforms provides a comprehensive set of capabilities that address the full scope of modern policy management.
Operationalizing Policies: Checklists vs. Questionnaires vs. Quizzes
The ecosystem clearly distinguishes between tools designed for different audiences and purposes, all derived from a single policy document.
- Actionable Checklists (for IT Teams): Generated by GeneratePolicy.com (3 tokens) or SecureCheck (unlimited with subscription), these documents translate policy requirements into implementation steps for technical teams.
- Compliance Questionnaires (for Auditors): Generated by GeneratePolicy.com (3 tokens), these are designed to help auditors verify that security controls described in a policy are active and functioning correctly.
- Interactive Quizzes (for Employees): Generated by PolicyQuest.diy, these are used to test and prove that employees have read and understood the policy content.
A Detailed Comparison: GeneratePolicy vs. SecureCheck Checklists
Feature | GeneratePolicy.com Checklist Tool | SecureCheck |
Primary Role | Add-on to Policy Generation | Dedicated Compliance Workflow Tool |
Pricing Model | Token-based (~$1.68 - $2.97 per item) | Subscription ($24/month) |
Volume Limit | Pay per checklist | Unlimited Checklists |
Input Source | Primarily the policy just generated | Any existing policy (PDF/Text) or Custom |
Ideal User | Small teams needing a quick start | CISOs/IT Teams managing full compliance |
Economic Models and Cost-Benefit Analysis
The platforms offer significant cost savings over traditional methods and provide flexible pricing models to suit different organizational needs.
GeneratePolicy.com Token Economics
The per-policy cost on GeneratePolicy.com decreases significantly with bulk token purchases, making it scalable for organizations of all sizes. The platform's cost is a fraction of the typical 300–1,000 cost for a single consultant-written policy.
Plan | Price | Total Tokens | Cost/Token | Policies Covered | $/Policy | Cost/Checklist |
Starter | $99 | 100 | $0.99 | 10 | $9.90 | $2.97 |
Professional | $399 | 600 | $0.66 | 60 | $6.65 | $1.98 |
Enterprise | $1,299 | 2,300 | $0.56 | 230 | $5.65 | $1.68 |
The Integrated Workflow and Its Impact
The true value of this ecosystem lies in its integrated, cyclical workflow, which creates a self-reinforcing loop of improvement based on actual usage data.
- Generate: A compliance team uses GeneratePolicy.com to create framework-aligned policies.
- Validate: The policies are converted into interactive training modules using PolicyQuest.diy.
- Analyze: Quiz results are analyzed to identify comprehension gaps, while the AI simultaneously spots outdated security principles in the text.
- Improve: The policy is updated by merging AI suggestions or regenerating it, and the cycle repeats.
This approach transforms policy management from a static project into a dynamic process. As one source describes it, traditional policy management is like using a printed paper map—it becomes outdated the moment it's printed. This AI-powered ecosystem functions like a modern GPS navigation system, providing a custom route (policy generation), turn-by-turn instructions (checklists), and real-time feedback to ensure the destination (compliance and security) is reached effectively.